Executive Summary: Every lending compliance team has the same fear: an examiner asks for verification records, and the answer is a filing cabinet, a shared drive full of PDFs with no timestamps, or worse, nothing at all. Building a compliance audit trail with API data replaces that uncertainty with a structured, timestamped, automatically generated record of every verification decision. This guide covers the regulatory requirements, the data architecture, and the practical steps CTOs and compliance officers need to move from manual paper trails to automated, exam-ready audit systems.
What Constitutes a Compliance Audit Trail in Lending?
A compliance audit trail is a tamper-resistant, chronological record that lets an independent reviewer reconstruct events: who performed a verification, what data was returned, when it happened, and what decision followed.[1] In lending, this applies to every step of the borrower verification process, from entity status checks through beneficial ownership confirmation to sanctions screening.
What Data Elements Does an Audit Trail Require?
The five core elements of a defensible audit trail are:[2]
• User attribution. The person or system identity that initiated the verification action.
• Timestamps. ISO 8601 formatted date and time for every event, establishing chronological order.
• Source data. The raw verification result, including the data source (e.g., state Secretary of State database, IRS records, OFAC SDN list).
• Decision logs. The outcome of the verification: approved, flagged for review, or declined, and the rule or policy that triggered the decision.
• Integrity controls. Evidence that the record has not been altered after creation, whether through checksums, immutable storage, or write-once database configurations.
For lending specifically, this means every entity verification, every sanctions screening, and every identity check must produce a record that ties the applicant, the data returned, and the underwriting decision together with a timestamp. When an examiner asks "How did you verify this borrower was a legitimate, active business on the date you funded the loan?", the audit trail must answer that question without ambiguity.
Why Do Manual Audit Trails Fail Examinations?
Manual verification processes create documentation gaps that are invisible until an exam exposes them. A compliance analyst manually navigating a state Secretary of State website, taking a screenshot, and saving it to a shared folder creates several failure points:
• No guaranteed timestamp. A screenshot's file metadata can be edited. Examiners know this.
• Inconsistent formatting. Fifty states, fifty different screenshot formats, no standardized data extraction.
• Missing records. When volume increases from 500 to 5,000 verifications per month, manual processes drop records.
• No chain of custody. There is no programmatic link between the verification result and the lending decision it supported.
"This was an area of the business that was completely manual still... sort of the Achilles heel." -- Joe Salvatore, Chief Risk Officer, Idea Financial
What Are the Regulatory Requirements for Audit Trail Retention?
Lending compliance officers operate under multiple overlapping record retention mandates. Understanding which rules apply to your institution determines how you architect your audit trail storage.
How Long Must BSA Records Be Retained?
The Bank Secrecy Act establishes the baseline: most BSA records must be retained for at least five years from the date of the transaction or the date the record was created.[3] This five-year floor applies to Customer Due Diligence (CDD) records, Suspicious Activity Reports (SARs), Currency Transaction Reports (CTRs), and the underlying verification documentation that supports them.
Under 31 CFR 1010.430, FinCEN's regulations establish this general five-year recordkeeping requirement for financial institutions subject to BSA obligations.[4] For lending institutions, this means every entity verification, every beneficial ownership check, and every sanctions screening result must be retrievable for a minimum of five years.
What Changed with OFAC's 10-Year Retention Rule?
In March 2025, the U.S. Treasury's Office of Foreign Assets Control published a final rule extending the recordkeeping requirement for sanctions compliance records from five to ten years.[5] This affects any lender conducting OFAC screening as part of their verification workflow.
The extended requirement applies to:[6]
• Blocked property records. Full records of each blocked transaction must be maintained for 10 years after the date the property is unblocked.
• Rejected transaction records. Complete records of each rejected transaction.
• OFAC screening results. Documentation of sanctions screening performed during onboarding and ongoing monitoring.
For alternative lenders integrating OFAC screening into their underwriting pipeline, this means the API response data from every sanctions check must be stored and retrievable for a decade, not just five years.
What Do State Regulators Expect?
State-level examinations add another layer. Non-bank lenders are subject to regulatory examinations that evaluate whether a company is following state laws and licensing rules, occurring on fixed schedules (every 2 to 5 years) or triggered by complaints and data anomalies.[7] States like California, New York, and Nevada conduct examinations that focus on rate caps, loan terms, consumer protection, and the documentation supporting lending decisions.[8]
New York's Department of Financial Services expects complete loan documentation, internal controls, and adherence to both state and federal lending laws.[9] The common denominator across all state examinations: can you produce a complete, timestamped record of the verification work you performed before funding a loan?
How Does SOC 2 Affect Audit Trail Architecture?
For CTOs evaluating verification vendors, SOC 2 compliance signals that the vendor maintains appropriate controls over data security, availability, and processing integrity. SOC 2 does not prescribe fixed data retention durations, but it requires organizations to define retention timelines based on business needs and applicable laws, and to demonstrate that confidential information is protected across its entire lifecycle.[10]
Under SOC 2's Processing Integrity criteria, detailed logs of all key processing activities, changes, and error corrections with timestamps are expected.[11] When selecting a verification API provider, the question is not just "Does this vendor have SOC 2?" but "Does this vendor's API produce the data I need to build my own audit trail?"
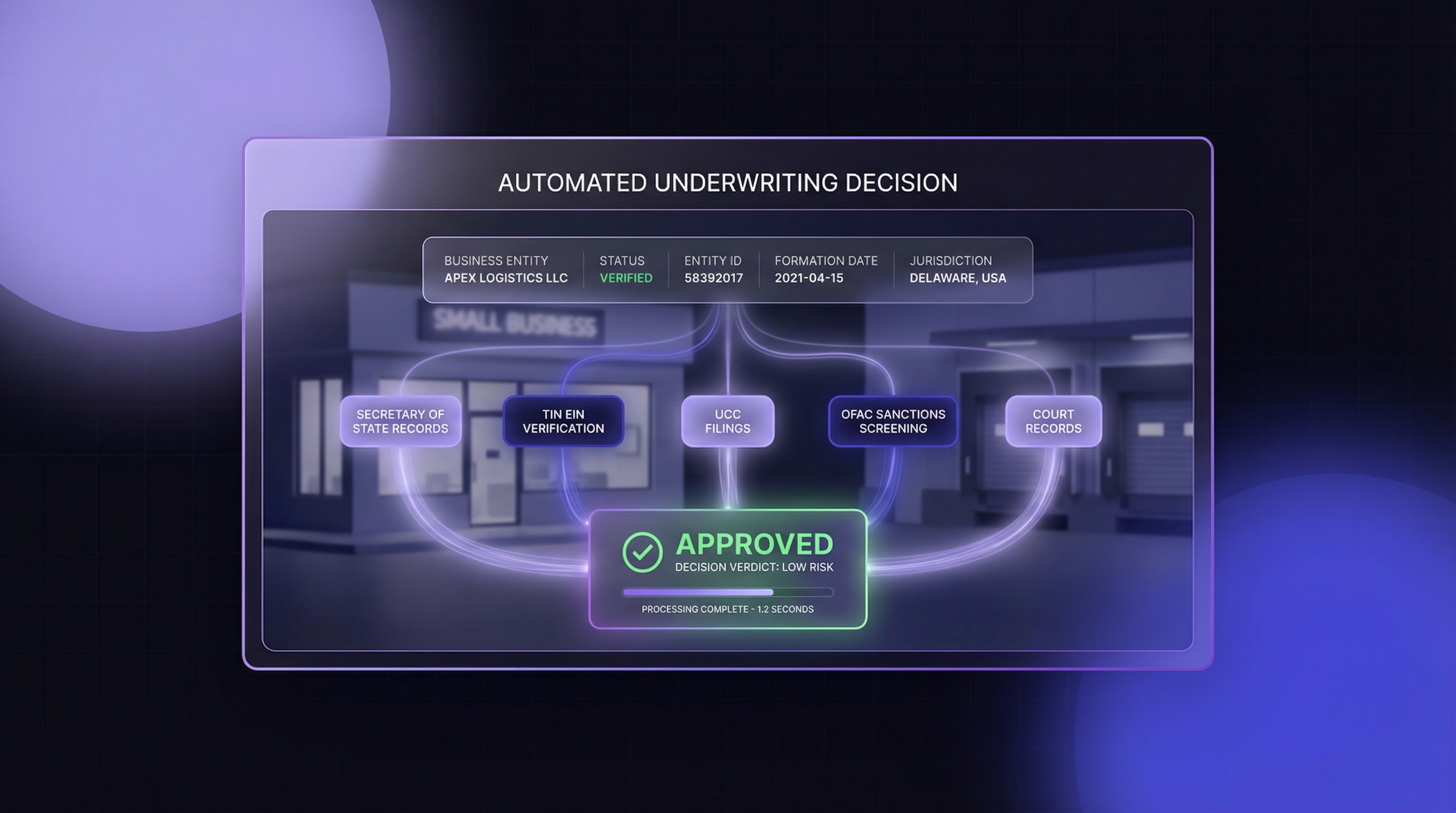
How Does API-Based Verification Create Automatic Audit Trails?
The fundamental shift from manual to API-based verification is this: every API call inherently generates a structured, timestamped record. There is no extra step to "create documentation." The documentation is the API transaction itself.
What Makes an API Response Audit-Grade?
An API response becomes audit-grade when it contains these elements:
• Unique request identifier. A `requestId` that links the verification event to a specific loan application.
• ISO 8601 timestamp. The exact date and time the verification was performed, generated server-side (not by the requesting system).
• Source identification. Which data source was queried (e.g., Delaware Secretary of State, IRS TIN database, OFAC SDN list).
• Complete result payload. The full data returned: entity status, officer names, filing dates, match scores.
• Visual proof. A timestamped screenshot of the source record at the moment of verification.
When a lender makes an API call to verify a business entity, the response contains all five elements in a single JSON payload. Store that payload, and you have an audit record that no examiner can dispute.
How Does This Compare to Manual Documentation?
| Element | Manual Process | API-Based Process |
|---|---|---|
| Timestamp | File metadata (editable) | Server-generated ISO 8601 (tamper-resistant) |
| Source proof | Screenshot saved to shared drive | Timestamped screenshot URL with watermark |
| Data format | 50 different state website formats | Normalized JSON, consistent across all states |
| Completeness | Depends on analyst diligence | Every field returned automatically |
| Searchability | Filename-based, manual lookup | Database-indexed by requestId, applicant, date |
| Chain of custody | No programmatic link to loan file | requestId maps directly to application record |
| Scalability | Breaks at high volume | Handles 10,000+ verifications per month |
What Integration Architecture Supports a Compliance Audit Trail?
Building an audit trail is not just about calling an API. It requires an architecture that captures, stores, indexes, and retrieves verification data in a way that satisfies examiners years after the original transaction.
How Should API Data Flow Into Your Compliance Database?
The following architecture diagram shows the data flow from verification request to audit-ready storage:
LENDING APPLICATION SYSTEM
|
| (1) Verification request triggered
v
+------------------+
| API GATEWAY | Your internal service that routes
| (Your System) | verification requests
+--------+---------+
|
| (2) API calls to verification endpoints
v
+------------------+ +------------------+ +------------------+
| SOS Verification | | TIN/EIN Verify | | OFAC Screening |
| (Entity Status) | | (Tax ID Match) | | (Sanctions Check)|
+--------+---------+ +--------+---------+ +--------+---------+
| | |
+------------+------------+------------+------------+
|
| (3) Raw API responses (JSON)
v
+---------------------------+
| AUDIT TRAIL PROCESSOR |
| - Attach loan application ID
| - Attach requesting user ID
| - Validate response completeness
| - Download & store screenshots
+------------+--------------+
|
| (4) Enriched verification record
v
+---------------------------+
| COMPLIANCE DATABASE |
| (Immutable Write-Once) |
| - Indexed by loan app ID |
| - Indexed by date range |
| - Indexed by entity name |
| - 5-10 year retention |
+------------+--------------+
|
| (5) On-demand retrieval
v
+---------------------------+
| EXAMINER EXPORT MODULE |
| - PDF report generation |
| - CSV/JSON data export |
| - Screenshot attachments |
| - Compliance summary view |
+---------------------------+What Are the Key Integration Components?
Step 1: Verification Request Trigger. Your loan origination system (LOS) or underwriting platform initiates verification when an application reaches the entity verification stage. The request should include the internal application ID, the requesting user, and the verification type.
Step 2: API Calls. Your API gateway calls the appropriate verification endpoints. For a standard alternative lending workflow, this typically includes SOS entity verification, TIN/EIN validation, and OFAC sanctions screening. Each call should request screenshots where available (`screenshot=true`).
Step 3: Response Capture. Every API response is captured in its raw JSON form. This is critical: do not transform or summarize the response before storing it. The raw payload is your primary audit evidence. Screenshots should be downloaded immediately and stored in your own object storage (S3, Azure Blob, GCS), because screenshot URLs from verification providers are typically temporary (3 to 30 days).
Step 4: Enrichment and Storage. The audit trail processor attaches your internal identifiers (loan application ID, requesting user, verification policy version) to the API response and writes the enriched record to an immutable, write-once compliance database. This database should support indexing by loan application ID, date range, and entity name.
Step 5: Examiner Export. When regulators request records, the export module generates formatted reports that include the verification data, screenshots, and a summary of the decision that followed each verification.
What Database Architecture Supports Long-Term Retention?
For the compliance database layer, consider these requirements:
• Write-once, read-many (WORM) storage. Prevents alteration of historical records. AWS S3 Object Lock, Azure Immutable Blob Storage, or database-level append-only tables.
• Partitioned by date. Enables efficient retention policy enforcement. Records older than 5 years (or 10 years for OFAC) can be archived to cold storage without affecting query performance.
• Full-text searchable. Examiners may request "all verifications for entity X" or "all verifications performed between date A and date B."
• Encrypted at rest. AES-256 encryption for stored verification data and screenshots. Required for SOC 2 compliance and industry best practice.
{
"auditRecord": {
"loanApplicationId": "APP-2026-04521",
"verificationTimestamp": "2026-03-19T14:32:07Z",
"requestedBy": "underwriter@lender.com",
"verificationType": "SOS_ENTITY_CHECK",
"apiRequestId": "abc123-def456",
"apiProvider": "cobalt_intelligence",
"state": "delaware",
"result": {
"entityName": "ACME FUNDING LLC",
"status": "Active",
"normalizedStatus": "active",
"filingDate": "2019-06-15",
"officers": ["John Smith - Manager"],
"confidenceScore": 0.95,
"screenshotUrl": "https://screenshots.cobaltintelligence.com/..."
},
"screenshotStoragePath": "s3://compliance-audit/2026/03/APP-2026-04521/sos-delaware.png",
"decisionOutcome": "PROCEED",
"policyVersion": "UW-POLICY-v4.2"
}
}What Makes Timestamped Screenshots a Compliance Differentiator?
Most verification providers return data. The question compliance officers should ask is: can you prove what the source record looked like at the exact moment you made the lending decision?
Why Do Examiners Value Visual Proof?
Structured data (JSON, XML) tells examiners what the system recorded. A timestamped screenshot of the actual Secretary of State webpage tells examiners what the state's official record showed. The screenshot serves as independent visual corroboration of the structured data.
This matters because:
• State databases change. A business that was "Active" on the date of funding may show "Dissolved" six months later when an examiner checks. Without a timestamped screenshot, the lender cannot prove the entity was active at the time of verification.
• Data intermediaries introduce lag. Secondary data providers (D&B, Experian, LexisNexis) aggregate from state sources with periodic refreshes. A screenshot from the primary source, timestamped to the minute, proves the lender verified against the most current data available.
• Screenshots are intuitive. Compliance officers and examiners can review a screenshot instantly. Parsing a JSON payload requires technical knowledge. Both should be in the audit file.
When API-based verification includes screenshots with date and time watermarks pulled directly from official state websites, it creates audit evidence that satisfies both technical and non-technical reviewers. JSON for the system, screenshots for the humans.
How Should Screenshots Be Stored for Long-Term Compliance?
Screenshot URLs from verification API providers are temporary. Cobalt Intelligence, for example, provides screenshot URLs valid for 3 to 30 days. Your integration must download and store these screenshots within that window.
Best practices for screenshot storage:
• Download immediately upon receiving the API response. Do not rely on retrieving screenshots later.
• Store in WORM-compliant object storage alongside the API response JSON.
• Name files systematically: `{loanAppId}/{verificationType}/{state}/{timestamp}.png`
• Include the screenshot storage path in the audit database record for retrieval.
• Apply the same retention policy as the underlying verification record (5 years minimum, 10 years for OFAC-related checks).
How Do You Build an Audit Trail Across Multiple Verification Types?
A single loan application typically requires multiple verification steps. The audit trail must capture each step independently while maintaining a unified view tied to the application.
What Does a Complete Verification Stack Look Like?
For alternative lenders processing merchant cash advances or business loans, the standard verification stack includes:
• Secretary of State entity verification. Confirms the business is registered and active. Returns entity status, filing date, officers, registered agent, and a timestamped screenshot. (1 credit per lookup)
• TIN/EIN verification. Confirms the business tax ID matches IRS records. Returns match/no-match with verification codes. (3 credits per lookup)
• OFAC sanctions screening. Checks the business and its principals against the Treasury's Specially Designated Nationals (SDN) list. Returns match scores. (1 credit per lookup)
• UCC filing data. Discovers existing liens and secured interests filed against the business. Available in 11 states. (1 credit per lookup)
• Court records. Identifies outstanding judgments and litigation. Available in New York and Miami-Dade County. (1 credit per lookup)
Each verification type generates its own API response with its own `requestId` and timestamp. Your audit trail processor groups these by loan application ID, creating a composite verification record.
How Do You Handle Asynchronous Verification Results?
Some verifications complete in seconds. Others, particularly live state lookups in slower states like Oregon (up to 5 minutes) or full multi-state searches across all 50 states, return results asynchronously via callback URLs or polling mechanisms.
Your audit trail architecture must handle both patterns:
• Synchronous results. Store immediately upon API response.
• Asynchronous results. Register a pending verification record when the request is made. Update it when the callback delivers results. The audit trail should show both the request timestamp and the result timestamp.
This distinction matters for examiners: it proves verification was initiated before the funding decision, even if the result arrived after a delay.
What Does the Before-and-After Look Like in Practice?
Before: Manual Paper Trail
A compliance analyst at a mid-size alternative lender processing 3,000 applications per month describes the manual process:
1. Receive application, identify the state of incorporation.
2. Navigate to that state's Secretary of State website (one of 50 different interfaces).
3. Search for the business by name. Hope the name matches exactly.
4. Take a screenshot of the result page. Save to a shared folder.
5. Manually type the entity status, filing date, and officer names into the loan file.
6. Repeat for TIN verification (call the IRS e-Services line or use a separate portal).
7. Repeat for OFAC screening (use the Treasury's SDN search tool).
8. File everything. Hope the folder structure makes sense in three years.
Result: 175+ hours per month in manual labor. Inconsistent documentation. Missing records discovered during examinations. No standardized format for examiners.[12]
After: Automated API Audit Trail
The same lender after integrating verification APIs:
1. Application enters the underwriting queue.
2. The LOS triggers automated verification: SOS entity check, TIN validation, OFAC screening.
3. API responses (JSON + timestamped screenshots) are captured and stored in the compliance database.
4. Business rules evaluate the results: active entity + TIN match + no OFAC hits = proceed. Any flag = route to manual review.
5. The complete verification record, including every API response, every screenshot, and the decision outcome, is indexed by loan application ID.
6. When an examiner requests records, the export module generates a formatted report in seconds.
Result: Verification completed in seconds instead of minutes. Every record has a server-generated timestamp. Screenshots prove what the state record showed at the moment of decision. Examiner requests answered in minutes, not days.
How Do You Get Started with API-Based Audit Trails?
What Should CTOs Prioritize in the Integration?
1. Start with the highest-risk verification. SOS entity status is the foundation. If the business is dissolved or inactive, nothing else matters.
2. Implement screenshot storage on day one. Do not defer this. Screenshot URLs expire. Build the download-and-store pipeline before going live.
3. Use immutable storage from the start. Retrofitting WORM compliance onto an existing database is expensive. Design for it upfront.
4. Index by loan application ID. Every verification record must be retrievable by the loan it supported.
5. Build the examiner export early. If you cannot produce a formatted report from your audit database, the database is not serving its compliance purpose.
Integration with a verification API provider like Cobalt Intelligence typically takes 3 to 5 days. The API follows RESTful conventions with JSON responses and standard API key authentication, and test mode is available for development without consuming credits.
Explore Cobalt Intelligence's API documentation to see the verification data and timestamped screenshots your audit trail will capture.
What Should Compliance Officers Validate?
Before approving a verification API integration, compliance officers should confirm:
• Record retention alignment. Does the integration architecture support 5-year BSA retention and 10-year OFAC retention?
• Screenshot permanence. Are screenshots downloaded and stored in your system, or are you relying on temporary vendor URLs?
• Data completeness. Does the API response include all fields needed for CDD documentation: entity status, formation date, officers, registered agent?
• Examiner readiness. Can you generate a complete verification report for a single loan application within minutes?
• Audit independence. Are verification records stored in write-once storage that prevents alteration?
Request a compliance-focused demo to see how timestamped SOS screenshots and normalized verification data map to your examination requirements.
How Does This Fit Into Your Broader Compliance Automation Strategy?
An API-based audit trail for business verification is one component of a larger compliance automation architecture. It connects directly to:
• BSA/AML compliance automation. Entity verification data feeds into your Customer Due Diligence (CDD) and Enhanced Due Diligence (EDD) programs. For a deeper look at automating BSA compliance for alternative lenders, see Compliance Automation for Alternative Lenders: BSA/AML.
• OFAC screening integration. The same audit trail architecture that captures SOS verification results also captures sanctions screening results, with the 10-year retention requirement applied automatically. For more on integrating OFAC screening into your underwriting workflow, see Don't Fund a Sanctioned Entity: Integrating OFAC Screening Into Your Underwriting.
• Ongoing monitoring. The audit trail is not just for onboarding. Periodic re-verification of existing borrowers creates new audit records that document your ongoing monitoring program.
The goal is a single, unified compliance database where every verification event, whether at origination or during portfolio monitoring, is captured with the same structure, the same timestamps, and the same visual proof.
Talk to Cobalt Intelligence's team about building a verification stack that covers SOS, TIN, OFAC, UCC, and court records through a single API integration.




.png)






.png)