Executive Summary: If you run compliance at an alternative lender processing thousands of deals per month, you already know the basics. You have a BSA program. You screen against OFAC. You file SARs. The problem is not awareness of the requirements. The problem is building compliance infrastructure that holds up under examination when your deal volume is 8,000 applications a month, your team is five people, and your state licensing obligations span 15 jurisdictions. This guide covers the operational compliance challenges that experienced compliance officers actually face: building defensible risk-based CDD procedures under FinCEN's 2026 exceptive relief, writing SAR narratives at scale without sacrificing quality, managing multi-state licensing workflows, and learning from recent examination findings and consent orders.
Building Risk-Based CDD Procedures Under FinCEN's 2026 Exceptive Relief
On February 13, 2026, FinCEN issued Order FIN-2026-R001, granting exceptive relief that allows covered financial institutions to collect beneficial ownership information "only as needed based on a covered financial institution's risk-based procedures for conducting ongoing customer due diligence," rather than at every new account opening.[1] Many compliance officers read this as permission to relax. It is the opposite. The order shifts the burden from a mechanical trigger (new account = collect BO) to a judgment-based trigger (your risk procedures determine when to collect BO). That means your procedures are now the thing examiners will scrutinize.
Step 1: Document Your Risk Tiering Methodology
Your CDD procedures need a written risk tiering framework that assigns every new applicant to a risk tier before the onboarding decision. At minimum, your framework should account for:
• Entity type and structure. Single-member LLCs with a registered agent as the only listed officer are higher risk than a 20-year-old corporation with named officers on state records. Complex multi-layer holding structures, particularly those involving out-of-state formations with no presence in the operating state, require enhanced scrutiny.
• Industry and product type. FinCEN's own risk assessment guidance identifies cash-intensive businesses, money services businesses, third-party payment processors, and marijuana-related businesses as elevated risk categories.[2] For MCA providers, add restaurants, auto dealers, and trucking companies, where fraud rates are historically elevated.
• Geographic risk. The entity's state of formation versus its state of operation matters. A Delaware LLC operating exclusively in Florida with a virtual registered agent and no physical presence is a different risk profile than a California corporation headquartered at a verified address.
• Transaction profile. Requested funding amount relative to the business's apparent size, time in business, and revenue history. A two-month-old LLC requesting $500,000 in MCA funding is categorically different from a five-year-old business requesting $50,000.
Step 2: Define BO Collection Triggers by Risk Tier
Under the exceptive relief, you are not required to collect beneficial ownership information for every applicant. But you must be able to defend exactly when you do and do not collect it. A defensible framework looks like this:
• Standard risk. Collect a certification of beneficial ownership with the application. Accept applicant-provided information unless red flags emerge during verification.
• Elevated risk. Collect BO certification, then independently verify ownership claims against Secretary of State records, corporate filings, and formation documents. If the entity has been formed within the last 12 months, verify the registered agent and principal address.
• High risk. Full BO verification including ownership chain analysis. For entities with multiple layers (LLC owned by another LLC), trace the chain until you reach a natural person holding 25% or more. Document every step of the analysis.
The key point: you need to show examiners that your triggers are consistent, applied uniformly, and not ad hoc. If your risk-tiering worksheet says "elevated risk = independent BO verification" but your files show that you skipped verification on 40% of elevated-risk applicants during a high-volume month, that is an MRA waiting to happen.
Step 3: Build the Verification Workflow
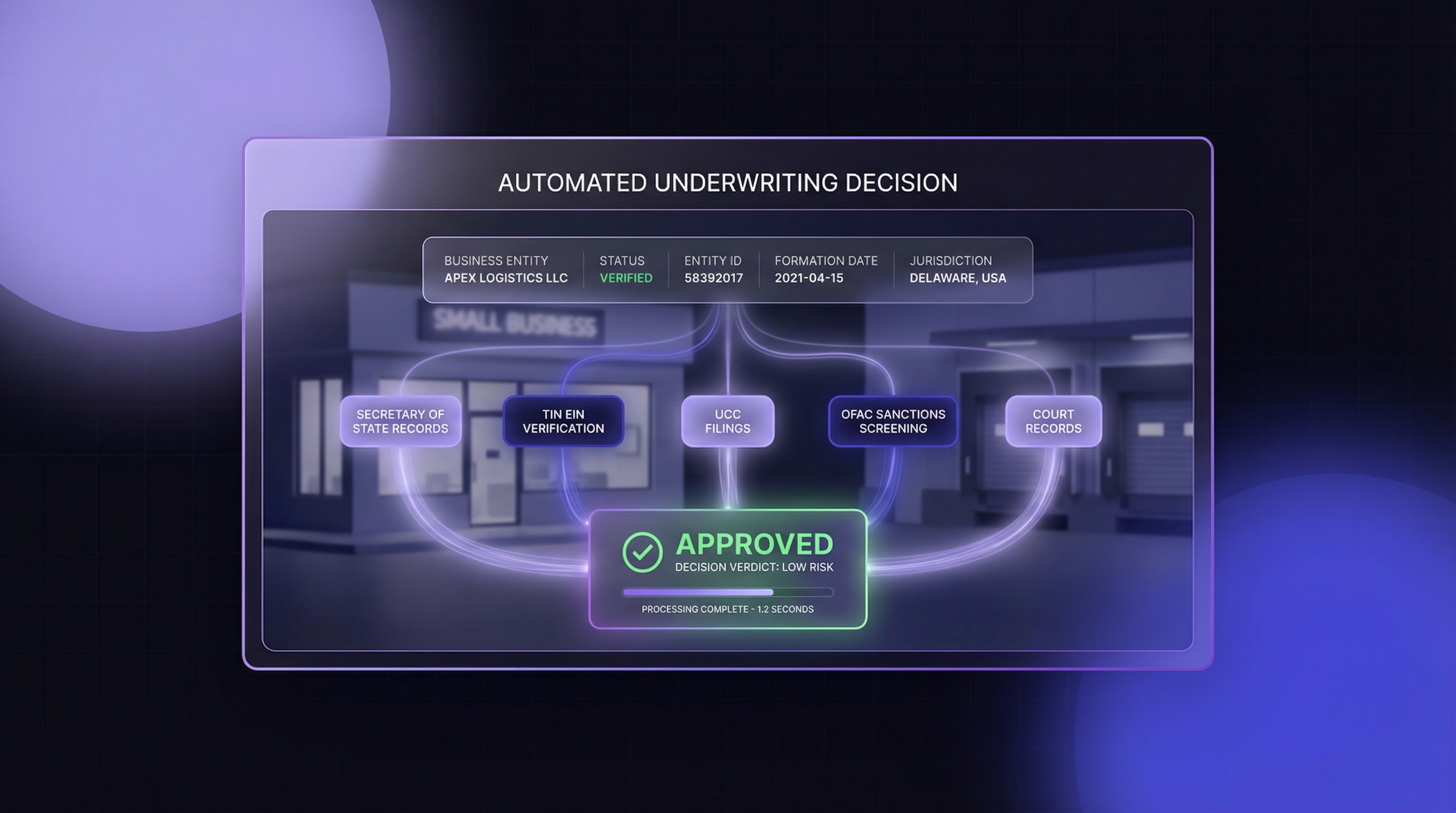
Risk-based CDD is only defensible if the verification itself is documented. Entity verification tools (Cobalt Intelligence, Middesk, Alloy, or direct state website lookups) should produce timestamped records showing what data was pulled, when, and from what source. The verification record needs to answer three questions an examiner will ask:
1. Did the entity exist and was it in good standing at the time of onboarding?
2. Did the officers/ownership information match what the applicant provided?
3. Were there any discrepancies, and if so, how were they resolved?
For lenders processing thousands of applications, API-based verification is the only practical way to produce this documentation consistently. Manual lookups across 50 state websites with different interfaces and formats introduce errors and gaps that are visible during examination.
Step 4: Ongoing Monitoring and Trigger Events
The CDD Rule's fourth pillar, ongoing monitoring, is where most alternative lenders have the weakest documentation. FinCEN expects that you are not just screening at onboarding but monitoring for changes. Trigger events that should prompt re-verification include:
• Renewal or re-funding. If a borrower comes back for additional funding after 12 months, re-verify entity status and BO information.
• Adverse media or screening hits. If a periodic OFAC re-screen produces a new match, or if adverse media surfaces, escalate and re-verify.
• Material change in transaction pattern. A borrower whose monthly processing volume doubles or whose industry classification changes warrants updated risk assessment.
• State filing changes. Administrative dissolution, officer changes, or registered agent changes detected through monitoring are trigger events.
Document every trigger event and the resulting action in the compliance file. The absence of documentation is treated the same as the absence of the action.
SAR Narrative Writing at Scale: Frameworks for High-Volume Lenders
Filing SARs is not the hard part. Writing defensible SAR narratives when you are processing 8,000+ deals a month and your SAR filing volume runs 30 to 50 per month is a fundamentally different operational challenge than writing five SARs a quarter. Quality degrades under volume pressure, and examiners can tell.[3]
The Triage Framework: When to File vs. When to Document and Close
Not every suspicious indicator warrants a SAR. FinCEN's threshold is activity that the institution "knows, suspects, or has reason to suspect" involves funds derived from illegal activity, is designed to evade BSA requirements, or lacks a lawful purpose.[4] But in high-volume alternative lending, you encounter low-level indicators constantly: mismatched addresses, recently formed entities, applicants who withdrew after identity verification was requested.
A defensible triage framework categorizes suspicious indicators into three tiers:
Tier 1: Mandatory filing. Clear indicators of fraud, structuring, or sanctions evasion. Examples: confirmed identity theft, applicant name matches OFAC SDN list, documented stacking across multiple funders, evidence of bank statement manipulation. File within 30 days of detection. No judgment call needed.
Tier 2: Enhanced review before filing decision. Ambiguous indicators that require additional investigation. Examples: entity formed within 30 days of application with no visible business operations, significant discrepancy between stated revenue and bank statement deposits, applicant operating in a high-risk industry with minimal verifiable history. Assign to a senior analyst. Document the enhanced review. Decision to file or close must be made within 15 business days.
Tier 3: Document and monitor. Low-level indicators that, standing alone, do not rise to suspicious activity. Examples: minor address discrepancy, registered agent change within the last 90 days, applicant declined to provide supplemental documentation but had otherwise clean verification. Create a case note in the compliance system. If the same borrower accumulates three or more Tier 3 indicators across transactions, escalate to Tier 2 review.
The critical discipline: document Tier 3 closures with the same rigor as Tier 1 filings. Examiners review closed cases to evaluate whether your triage standards are consistent. "We investigated and determined no SAR was warranted" is defensible. An empty file with no documentation of the analysis is not.
SAR Narrative Templates for Common Alternative Lending Scenarios
FinCEN's guidance on SAR narrative quality emphasizes five elements: who, what, when, where, and why. At scale, narrative templates ensure consistency without turning SAR writing into a fill-in-the-blank exercise. The narrative must tell a coherent story, not just list facts.[5]
Template structure for MCA/alternative lending SARs:
Paragraph 1: Subject identification and relationship. State the subject's name, entity type, state of formation, date of formation, the product applied for, and the date of application. Include the applicant's stated business type and time in business.
Paragraph 2: The suspicious activity. Describe what triggered the investigation, using specific dates, amounts, and facts. "On [date], during entity verification, [specific finding] was identified" is stronger than "the applicant's information appeared suspicious." Reference the specific verification data: Secretary of State status, TIN match result, officer discrepancy, OFAC screening result.
Paragraph 3: Investigation and corroborating information. Describe what additional steps were taken. Did you verify against state records? Check UCC filings? Review bank statements? Cross-reference with other applicants in your system? Include results of each step.
Paragraph 4: Disposition. State whether funding was approved or declined, whether the relationship was terminated, and whether law enforcement was contacted.
Paragraph 5: Supporting documentation. List all documents and records preserved in the case file, including verification screenshots with timestamps, correspondence, and internal review notes.
Volume Management: Staffing and Quality Control
At 30+ SARs per month, you need a quality control layer. Best practice for high-volume shops:
• Separation of duties. The analyst who identifies the suspicious activity should not be the same person who writes the final narrative and approves filing. At minimum, a senior BSA analyst or the BSA officer should review and approve every SAR before submission.
• Batch filing discipline. FinCEN's 30-day filing window (from date of initial detection) is absolute. Track detection dates in your case management system and build automated alerts at day 15 and day 25.
• Continuing activity SARs. For ongoing suspicious activity involving the same subject, file continuing SARs every 90 days as required. Track these separately from initial SARs, because the narrative requirements differ: continuing SARs must reference the original SAR by BSA ID and describe what has changed.[6]
• Quality metrics. Track rejection rates from FinCEN (malformed filings), average time from detection to filing, and narrative completeness scores from internal review. If your rejection rate exceeds 5%, your templates or training need revision.
Multi-State Licensing Workflow for Alternative Lenders
State licensing is the compliance obligation that catches the most alternative lenders off guard, because the requirements are fragmented, inconsistent, and aggressively enforced.[7]
Which States Require Licensing for MCA and Alternative Lending?
The licensing landscape depends on your product type. A simplified overview of the current state:
States requiring commercial lending/financing licenses: California (CFL or CDDTL), Connecticut, Florida, Georgia, Illinois, Maryland, Nevada, New Jersey, New York, Utah, Virginia.
States with commercial financing disclosure requirements: Eleven states now have disclosure laws on the books: California, New York, Utah, Virginia, Georgia, Florida, Connecticut, Kansas, Missouri, Louisiana, and Texas (effective December 31, 2026).[8]
States where MCA-specific requirements are evolving: New York's commercial financing disclosure requirements under SB 5470 include MCA transactions. California's SB 825, effective January 1, 2026, expanded the DFPI's authority to enforce provisions against deceptive or abusive acts by licensed finance lenders.[9] Virginia's commercial financing disclosure rules went into effect in 2023. Utah's requirements apply to "commercial financing" broadly, which includes revenue-based financing.
The challenge is that "commercial lending license" means different things in different states. Some states exempt certain transaction types (true merchant cash advances based on purchased receivables may be treated differently than loans in some jurisdictions). Others require licensing regardless of product structure. Legal counsel with state-by-state expertise is not optional.
License Renewal Tracking and Exam Preparation
Missing a license renewal deadline can trigger automatic license suspension. For a lender licensed in 12 states, tracking renewal dates, annual report filing deadlines, call report due dates, and surety bond renewal dates across all jurisdictions is a significant operational burden.
Build a licensing compliance calendar that tracks:
• Renewal dates by state. Most states operate on an annual cycle, but the dates vary. California's CFL annual report is due March 15. New York's MCA registration renewal operates on a different cycle. NMLS-managed licenses may have unified renewal windows (November 1 through December 31 for most).
• Call report and annual report deadlines. Many states require quarterly or annual financial reporting. Late filings generate automatic flags and can trigger examination.
• Surety bond amounts and renewal dates. States that require surety bonds (California, Georgia, Connecticut, among others) will suspend your license if the bond lapses.
• Registered agent and office requirements. Some states require a physical office or registered agent within the state. Changes must be reported within defined windows, typically 30 days.
NMLS (Nationwide Multistate Licensing System) manages licensing for many states, but not all alternative lending license types are on NMLS. Maintain a parallel tracking system for non-NMLS licenses.
Common Exam Findings in Alternative Lending Compliance
State examiners have become significantly more sophisticated about alternative lending operations over the past three years. The days of examiners who did not understand MCA product structure are largely over. Here are the findings that appear most frequently in examination reports and consent orders:
1. Inadequate BSA/AML programs relative to risk profile. The most common MRA. Examiners compare your deal volume and product complexity to your compliance infrastructure. If you process 8,000 deals per month with a two-person compliance team and no automated screening, expect this finding. The examiner is looking for evidence that your compliance resources are proportional to your risk.[10]
2. Incomplete or inconsistent CDD files. Examiners pull a sample of files (typically 20 to 50) and look for completeness. Missing entity verification documentation, unsigned BO certifications, or verification records that cannot be tied to a specific date and time are findings. This is where timestamped API responses and verification screenshots from tools like Cobalt Intelligence or Middesk demonstrate their value: they produce consistent, dated records for every file.
3. SAR filing deficiencies. Common sub-findings include: SARs filed outside the 30-day window, narratives that lack specificity ("applicant appeared suspicious" with no supporting detail), failure to file continuing SARs for ongoing activity, and inconsistent application of filing thresholds across analysts.
4. Disclosure violations. In states with commercial financing disclosure requirements, examiners verify that disclosures were provided at the correct point in the transaction, that the content matches regulatory requirements, and that records of disclosure delivery are maintained. California's disclosure requirements under SB 1235 (now codified) have specific formatting and content rules that examiners check against.
5. Advertising and marketing compliance. Examiners review your website, marketing materials, and sales scripts for compliance with state-specific advertising rules. Claims about approval speed, guaranteed funding, or interest rate comparisons are frequently cited.
Recent Enforcement Actions and Lessons for Alternative Lenders
Studying consent orders and enforcement actions reveals patterns that compliance officers can use to stress-test their own programs.
TD Bank: $3 Billion Penalty for Systemic AML Failures (2024)
TD Bank's penalty included $1.8 billion from the DOJ, $1.3 billion from FinCEN, and $450 million from the OCC for enabling drug trafficking by ignoring red flags in high-volume suspicious transactions.[11] The lesson for alternative lenders is not about the headline number. It is about what the consent order revealed: TD Bank's transaction monitoring system was deliberately configured to exclude certain transaction types from review. The institution knew its monitoring had gaps and chose not to close them. Examiners look for the same pattern at smaller institutions: monitoring rules that have known blind spots, alert thresholds that have not been recalibrated as business volume increased, and suspicious activity reports that stop at the obvious fraud without investigating the broader pattern.
OKX: $504 Million for AML Program Failures (2025)
OKX, a cryptocurrency exchange, paid over $504 million after pleading guilty to failing to maintain an effective AML program.[12] The core failure was not the absence of a program. It was that the program was not designed to match the institution's actual risk. The exchange operated in high-risk geographies, processed high-value transactions, and served customers with minimal identity verification, but its AML controls were built for a lower-risk business model. For alternative lenders, the parallel is clear: a compliance program designed for 500 deals per month does not scale to 5,000 without structural changes to monitoring, staffing, and technology.
State-Level Actions Against Alternative Lenders
State regulators have been increasingly active against non-bank lenders. The California DFPI has issued multiple enforcement actions against commercial lenders for licensing violations, disclosure failures, and unfair lending practices. In 2025, the DFPI ordered a commercial lender to pay restitution and civil penalties exceeding $2 million for operating without a required CFL license and failing to provide required disclosures.[13] New York's DFS has similarly targeted MCA providers for disclosure violations and has used its broad authority under the Martin Act to pursue lenders whose practices it deems deceptive.
The consistent pattern across state enforcement: regulators are not just checking whether you have a license. They are examining whether your operational practices match your compliance representations. If your compliance manual says you verify entity status for every applicant but your files show that verification was skipped during high-volume periods, the gap between policy and practice becomes the finding.
Non-Financial Costs That Matter More Than Fines
For most alternative lenders, the existential risk from compliance failure is not the fine itself. It is the downstream consequences:
• Loss of banking relationships. Banks are de-risking by terminating correspondent and sponsorship relationships with alternative lenders that cannot demonstrate adequate compliance programs. Without a banking partner, a lender cannot fund deals.
• Consent orders and MRAs. Matters Requiring Attention impose operational restrictions that can take years to resolve. A consent order may require board-level reporting, independent compliance testing, and prior approval for new products or geographic expansion.
• Personal liability. FinCEN has assessed civil money penalties against individual BSA officers, not just institutions. Senior compliance personnel can face individual penalties for willful violations.[14]
• Reputational damage. Enforcement actions are public records. Prospective borrowers, investors, banking partners, and potential acquirers perform due diligence. A FinCEN action on your record changes every conversation.
Building the Compliance Automation Stack
Manual compliance workflows do not scale beyond about 2,000 applications per month without significant staffing increases. For lenders processing higher volumes, automation is an operational necessity.
The compliance automation stack for alternative lenders typically includes these layers, and no single vendor covers all of them:
Entity verification and KYB data. Real-time business entity data from Secretary of State records, including status, officers, formation date, and registered agent. Providers include Cobalt Intelligence (primary source, real-time state website data with screenshots), Middesk (full-service KYB platform), and Alloy (identity and compliance orchestration). The differentiator is data freshness: primary source providers pull directly from state databases with each request, while aggregated databases like D&B and Experian may be days or weeks behind.
Sanctions and watchlist screening. OFAC SDN list screening, plus screening against other government watchlists. ComplyAdvantage, Dow Jones Risk & Compliance, and Refinitiv World-Check are the major providers. Some entity verification providers (including Cobalt Intelligence) also offer OFAC screening as part of their API suite. The critical requirement is not which provider you use but that you can produce an audit trail showing every applicant was screened, when, and what the result was.
Transaction monitoring and SAR management. Systems that flag suspicious patterns in transaction data and manage the SAR filing workflow. Hummingbird, Verafin (now Nasdaq), and Unit21 specialize in this space. For alternative lenders, the key capability is configurability: your transaction monitoring rules need to reflect MCA-specific risk patterns (stacking, rapid re-funding, split transactions), not just traditional banking patterns.
Compliance case management. Tracking investigations, SAR filings, licensing renewals, and examination preparation. This may be a module within your transaction monitoring platform or a separate system. The requirement is that every compliance decision is documented, dated, and auditable.
Identity verification. Verifying that the individual signing the application is who they claim to be. Socure, Jumio, Onfido, and others provide document verification and biometric matching. For compliance purposes, the verification record needs to tie to the specific transaction and be stored in the compliance file.
The mistake to avoid: treating compliance automation as a single vendor decision. No one platform covers entity verification, sanctions screening, transaction monitoring, identity verification, and SAR management with equal strength. The best compliance programs use specialized tools at each layer and integrate them through their core system of record.
The Corporate Transparency Act: Preparing for Regulatory Uncertainty
The Corporate Transparency Act remains in flux. In March 2025, FinCEN issued an interim final rule removing the requirement for U.S. companies to report beneficial ownership information, narrowing the obligation to entities formed under foreign law that have registered to do business in any U.S. state.[15] The Eleventh Circuit Court of Appeals affirmed the CTA's constitutionality in December 2025, and FinCEN is expected to issue a final rule in 2026.[16]
For compliance officers, the practical approach is to prepare for full implementation while operating under current requirements:
• The CDD Rule still applies independently. Regardless of the CTA's status, the FinCEN CDD Rule requires beneficial ownership verification for covered financial institutions. The CTA would have created a public registry; without it, the verification burden stays entirely with the lender.
• State-level action is not waiting. New York's LLC Transparency Act took effect January 1, 2026, requiring beneficial ownership disclosure for foreign-formed LLCs doing business in the state.[17] Other states may follow with similar requirements.
• Reinstatement risk. A future administration could rescind the interim final rule and reinstate full reporting requirements. Building verification workflows now means you will not be scrambling later.
Alternative lenders that already pull officer and ownership data from Secretary of State records during entity verification are positioned to meet beneficial ownership requirements under any regulatory scenario. The data is available; the question is whether your workflows capture and document it systematically.







.png)



.png)